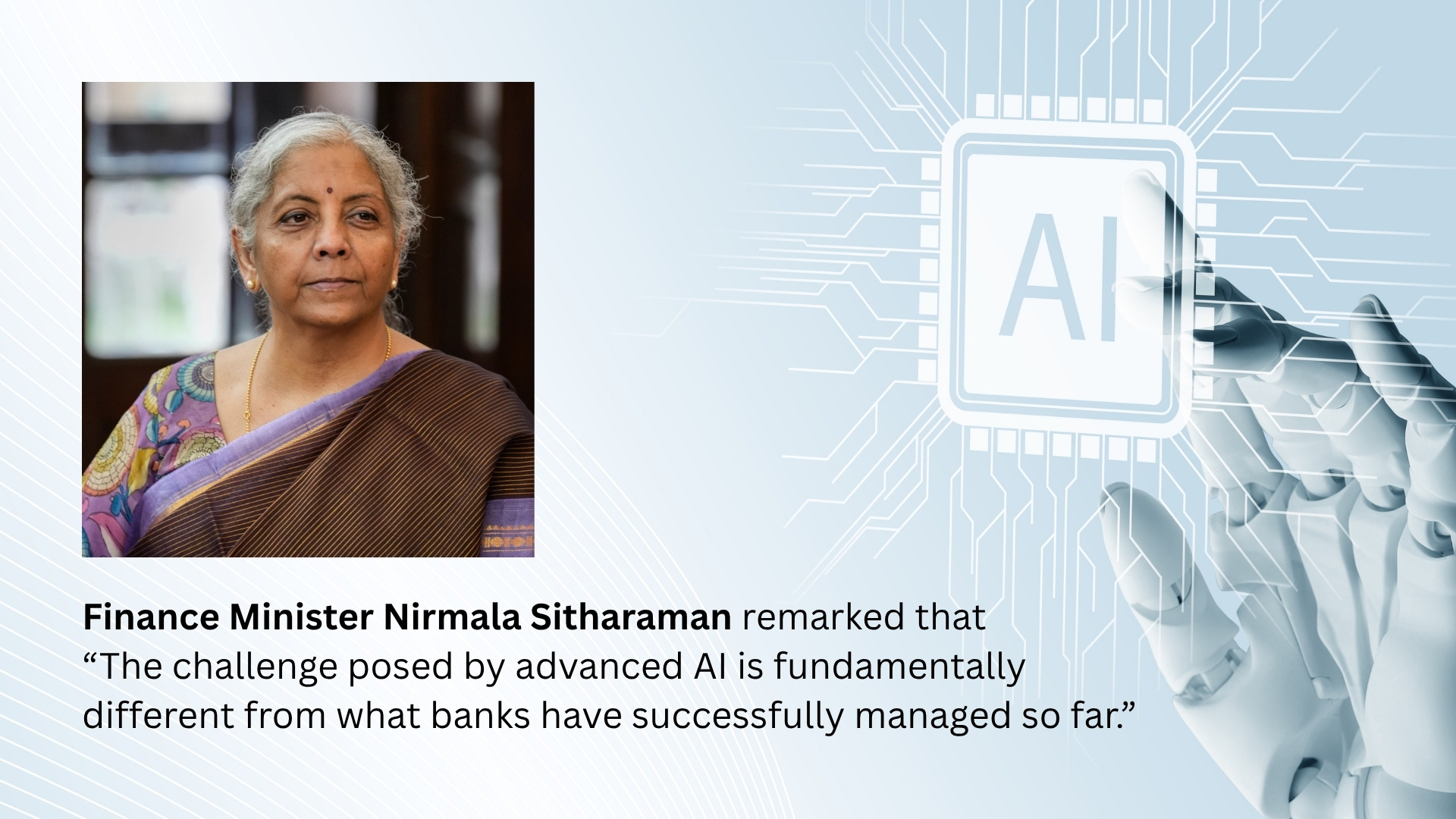
Corporate fraud in 2025 did not merely “move online”. It learned to operate like a digital business process. Fraud schemes increasingly mirrored legitimate workflows, exploiting payment rails, identity systems and insider access with a precision that traditional controls were never designed to detect. What emerged was a new doctrine of misconduct: faster execution, lower visibility and growing organisational ambiguity over where a “fraud incident” ends and a “cyber incident” begins.
This convergence fundamentally altered the risk landscape for Corporate India.
2025’s Digital Fraud Pivot
India’s fraud environment in 2025 was shaped by two reinforcing realities: explosive growth in digital transactions and an equally rapid evolution of attack and laundering ecosystems. Government disclosures underscored the magnitude of the challenge. Cyber-enabled financial fraud losses reported for 2024 stood at ₹22,845.73 crore, a 206 percent increase over the previous year, with over 36.37 lakh incidents recorded through national reporting platforms.
For corporate risk leaders, these numbers were not merely retrospective. They served as a leading indicator. If consumer-facing systems were under such intense pressure, enterprise payment workflows, vendor ecosystems and shared-service centres were inevitable next targets, with higher ticket sizes and more complex recovery challenges.
Banking sector data reinforced this shift. The Reserve Bank of India’s Annual Report 2024-25 showed a paradoxical trend: the number of fraud cases fell sharply to 23,953 from 36,060 in the previous year, but the total value of fraud surged to ₹36,014 crore from ₹12,230 crore. This divergence matters. Fraud risk is becoming barbelled, characterised by high-frequency, low-value digital fraud on one side and fewer but balance-sheet-threatening corporate frauds on the other.
Five Channels That Defined Corporate Fraud in 2025
The defining pattern of 2025 was not any single technique, but the orchestration of multiple vulnerabilities into seamless attack chains.
Payment diversion through Business Email Compromise (BEC) and invoice redirection remained a dominant vector. Fraudsters exploited lookalike domains, compromised mailboxes and vendor master data to reroute legitimate payments, often timed around quarter-end pressures. CERT-In explicitly flagged BEC and ransomware-linked credential compromise as financially motivated pathways, underscoring that email and identity layers remain primary battlegrounds.
Instant-payment rail abuse also spilled over from retail to corporate environments. RBI data shows UPI fraud cases rose sharply, with FY24 recording 13.42 lakh cases involving ₹1,087 crore, and FY25 already crossing 6.32 lakh cases involving ₹485 crore by September. The corporate risk lies less in volume and more in behavioural transfer: retail fraud scripts are now repackaged to target finance teams through urgency, impersonation and social engineering.
Mule accounts and laundering networks compressed recovery windows to minutes. Ministry of Home Affairs disclosures highlighted over 11 lakh suspect identifiers and more than 24 lakh mule accounts flagged through a national registry, preventing an estimated ₹4,631 crore in additional losses. For corporates, this means a single lapse can result in irreversible fund outflows before alerts even trigger.
Insider data leaks evolved into monetisation engines. SEBI’s Annual Report 2024-25 recorded penalties of ₹813.83 crore and 400 investigations, including 287 insider trading cases. Enforcement narratives increasingly acknowledge that unpublished price-sensitive information leaks through weak access controls and informal collaboration channels, not only deliberate tip-offs.
Finally, deepfake-enabled authorisation fraud moved from theory to practice. Globally documented cases, including a $25 million loss in Hong Kong following a deepfake video call, reinforced a hard truth: visual confirmation is no longer a reliable control when approvals are rushed and context is thin.
Red Flags Boards Repeatedly Missed
The most damaging red flags of 2025 were not exotic. They were governance blind spots hiding in plain sight. RBI’s fraud break-up highlights a critical asymmetry: digital payment frauds dominate by count, while advances-related fraud dominates by value. Large losses typically stem from weak beneficiary controls, over-privileged access, diluted maker-checker discipline and exception-heavy approval cultures.
Three warning signals recurred across sectors: identity risk driven by excessive access and weak email authentication, process risk created by high-trust approvals under time pressure and reporting latency that missed recovery windows despite improved national response mechanisms.
Lessons for 2026: From Policy to Performance
Fraud prevention in 2026 must be engineered as a real-time control system, not a quarterly compliance ritual. Payment governance must harden, with beneficiary changes locked behind multi-factor authentication, dual approvals, mandatory call-backs to verified contacts and cooling-off periods for new payees.
Insider-risk architecture must mature, reducing standing privileges, monitoring abnormal data access and integrating fraud, cyber and HR signals. Above all, boards must demand measurable readiness: time-to-detect, time-to-freeze funds and stress-tested response playbooks.
In a year when reported banking fraud value surged despite fewer cases, credibility in 2026 will hinge less on policy density and more on whether controls hold under pressure, at speed and across the extended enterprise ecosystem.
Published by RiskAwareness.in as part of its year-end risk insights series.